

A smart blend of people, process and technologies.
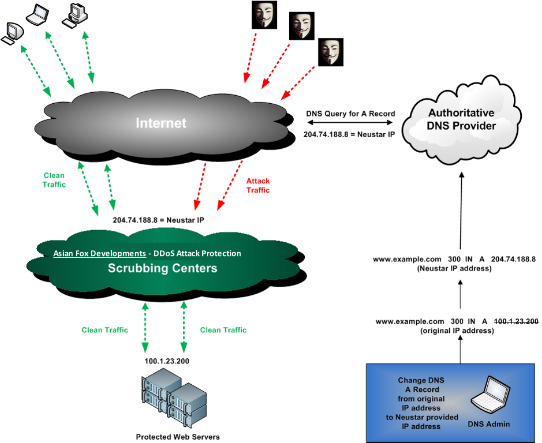
To mitigate DDoS attacks, Asian Fox Developments offers on-demand cloud-based protection service. You also have the option to add always-on hardware, plus real-time alerting and detection capabilities. It’s all backed by the experienced DDoS fighters in the Asian Fox Developments SOC, who bring years of experience and proven responses to every mitigation.
The Power of the Cloud
Local DDoS protection will only hold the fort so long. When attacks become super-sized, the Asian Fox Developments SiteProtect cloud offers the capacity to scrub bad traffic and keep your website up.
On-Demand or Always-On
With on-demand deployment, gain more control over mitigation and related costs. Activate via DNS redirection or BGP routing. If you experience frequent attacks, choose SiteProtect Hybrid with always-on Arbor Networks hardware installed on site, plus failover to the Asian Fox Developments cloud when attacks exceed capacity. SiteProtect Hybrid is fully managed by the Asian Fox Developments SOC.
24/7 DDoS Mitigation Experts
Asian Fox Developments 24/7 Security Operations Center is staffed by experts who offer years of frontline experience.
Affordable Fixed-Cost DDoS Protection
With SiteProtect, there’s no additional investment in hardware, software or staff. Our fixed-cost model protects your budget, no matter how big the attack.
Diverse Blend of DDoS Mitigation Technologies
With best-of-breed technologies from leading mitigation vendors, SiteProtect defends against the widest range of attacks.
A distributed denial-of-service attack (DDoS attack) is an attempt to make a computer resource unavailable to its legitimate users. In general terms, DoS attacks are implemented by either forcing the targeted computer(s) to reset, or consuming its resources so that it can no longer provide its intended service or obstructing the communication media between the intended users and the victim so that they can no longer communicate adequately.
Today’s many types of attacks fall into two main categories:
VOLUMETRIC ATTACKS
Flooding attacks. Saturates and consumes network bandwidth and infrastructure. Examples: ICMP, UDP or TCP Syn Floods.
APPLICATION LAYER ATTACKS
Harder to detect than Volumetric Attacks. Targets specific applications of services where they exhaust resources.
Examples : HTTP or DNS attacks.
Our system takes a layered approach that enable us to block both types of attacks.
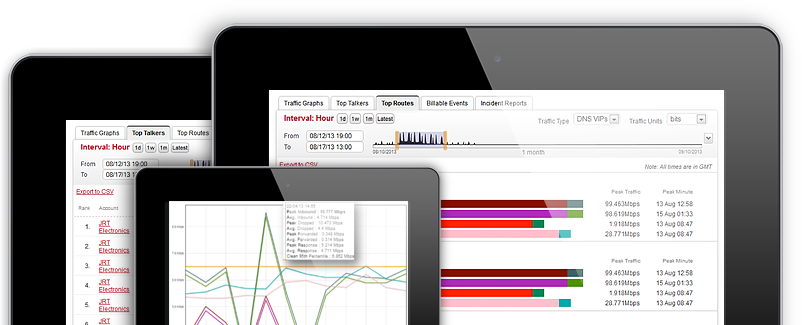
The Asian Fox Developments DoS Mitigation Service includes a web based user interface where users can view detailed information about their incoming and outgoing network traffic. Reports include: total traffic, traffic by application type, traffic by network protocol, traffic by country, ongoing DoS alerts, ongoing Mitigations, and detailed information regarding the DoS attack.
Interested? We know, you are interested! CONTACT US
